Why TLS v1.0 or v1.1 Cannot Be Used After the NGINX Ingress Controller Add-on Is Upgraded?
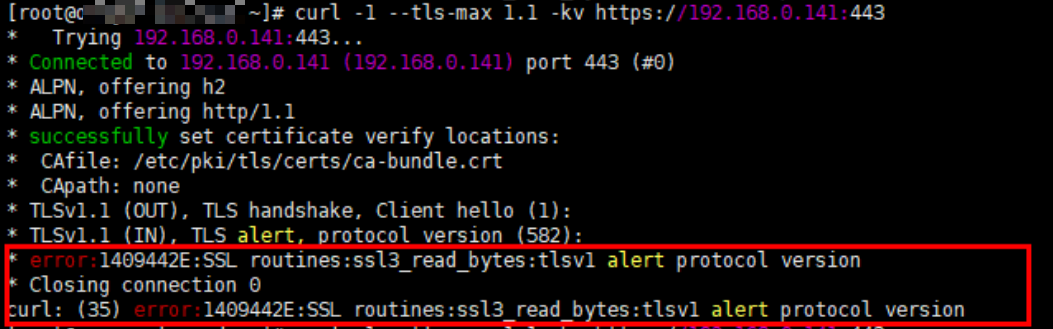
Symptom
After the NGINX Ingress Controller add-on is upgraded to 2.3.3 or later, if the TLS version of the client is earlier than v1.2, an error is reported during the negotiation between the client and NGINX Ingress Controller.
Solution
NGINX Ingress Controller 2.3.3 and later versions support only TLS v1.2 and v1.3 by default. If additional TLS versions are needed, you can add the @SECLEVEL=0 field to the ssl-ciphers parameter configured for the NGINX Ingress Controller add-on. For details, see TLS/HTTPS.
For secure data transmission, it is advised to avoid using TLS v1.0 or v1.1. These outdated protocols pose security risks that could lead to data leakage or be exploited by attackers. You are advised to upgrade TLS to v1.2 or later versions for enhanced communication security.
- Log in to the CCE console and click the cluster name to access the cluster console. In the navigation pane, choose Add-ons, locate the NGINX Ingress Controller add-on, and click Manage.
- Click Edit of the corresponding instance.
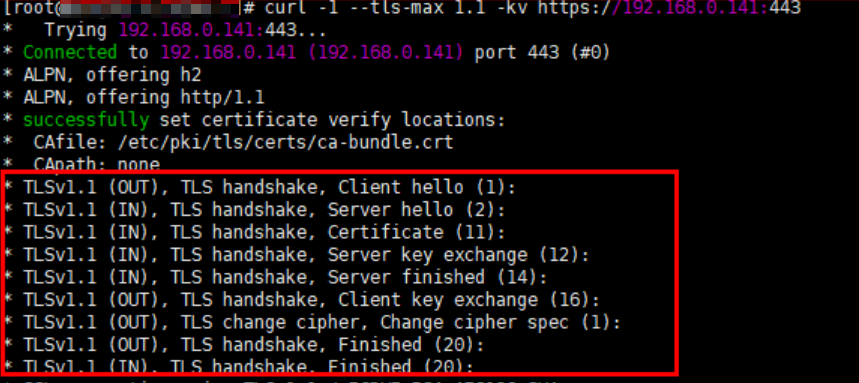
- Add the following configuration to the Nginx Parameters:{"ssl-ciphers": "@SECLEVEL=0 ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:DHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES256-SHA256:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:DES-CBC3-SHA","ssl-protocols": "TLSv1 TLSv1.1 TLSv1.2 TLSv1.3"}
- Click OK.
- Use TLS v1.1 for access again. The response is normal.
- Symptom
- Solution